Programming a security system is essential for customizing its functionality to meet specific security needs and preferences. Whether installing a new system or updating an existing one, understanding how to program the security system is crucial for maximizing its effectiveness. To begin, familiarize yourself with the control panel and user interface, accessing menus and settings for configuration.

Determine which sensors, detectors, and devices will be integrated into the system, assigning them unique zones and settings. Customize alarm triggers, entry/exit delays, and notification preferences according to desired security levels and operational requirements. This article aims to provide a comprehensive guide on how to program a security system.
Additionally, consider integrating additional features such as home automation, remote monitoring, and integration with third-party devices for comprehensive security management. By mastering the programming process, users can tailor their security system to provide reliable protection and peace of mind for their homes or businesses.
Importance of Programming a Security System
Programming a security system is more than a technical necessity; it’s a crucial step in ensuring the safety and security of a property. Customized programming allows homeowners and business owners to align the security system with their specific safety goals, lifestyle, and daily operations.
By precisely setting up sensors, cameras, and alarms, users can avoid false alarms, which often lead to unnecessary stress and potentially costly fines. Furthermore, tailored configurations ensure that in the event of an intrusion or emergency, the system reacts in the most efficient way possible, alerting the right parties immediately.
Personalized notification settings ensure that users are informed of security breaches in real-time, providing an opportunity to respond swiftly. Essentially, the careful programming of a security system enhances its efficacy, making it a proactive rather than a reactive tool in the prevention of security incidents.
Benefits of Understanding the Programming Process
Gaining an understanding of the programming process for a security system offers several significant benefits. First and foremost, it empowers users with the ability to make immediate adjustments to their system, ensuring that their security needs are continually met without the need for external assistance.

This autonomy can lead to significant cost savings over time, as users can perform routine maintenance and updates themselves. Additionally, a deep knowledge of how the system is programmed allows for more effective troubleshooting of issues as they arise, minimizing downtime and potential security vulnerabilities.
Beyond these practical advantages, familiarity with the programming process also enables users to take full advantage of their system’s capabilities. By understanding the system’s features and how they can be customized, users can create a security setup that is truly tailored to their personal or business needs.
This customization can extend to integrating the security system with other smart home devices, creating a cohesive, automated security and management ecosystem. Finally, knowing how to program and fine-tune a security system fosters a stronger sense of confidence and peace of mind, knowing that one’s property is protected by a system that is optimized for one’s specific environment and lifestyle.
Understanding Security System Components
A comprehensive understanding of the various components that make up a security system is foundational to effective programming and customization. Typically, a security system comprises a central control panel, which functions as the brain of the system, coordinating responses and communicating with all connected devices.

Sensors are another crucial component; these include door and window sensors, motion detectors, and glass break sensors, which are strategically placed around the property to detect unauthorized entry or movement. Cameras, both indoor and outdoor, provide visual surveillance, enabling real-time monitoring and recording of activities within and around the premises.
In addition to the basic components, environmental sensors add another layer of protection, detecting smoke, carbon monoxide, water leaks, and significant temperature changes, thereby safeguarding against more than just unauthorized access.
Key fobs and access control systems offer convenient ways to arm or disarm the system, restrict access to certain areas, and manage entry for both residents and visitors. Lastly, an integrated communication system, which may include cellular, Wi-Fi, or landline connections, ensures that the security system can alert homeowners and monitoring services to potential threats, regardless of the property’s occupancy at the time of the incident.
By familiarizing oneself with each of these components and their functionalities, users can better understand how to program their security system effectively, ensuring a customized, robust defense against a wide array of security threats.
Overview of Security System Components
The effectiveness of a security system hinges on the seamless integration and programming of its key components, each serving a distinct, critical role in the overall security framework. This overview will delineate the primary components that constitute the backbone of a comprehensive security system:
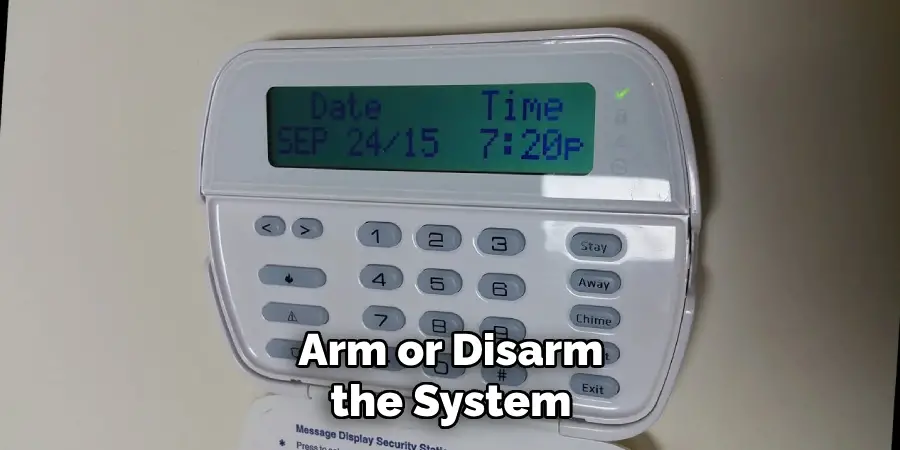
- Control Panel: The epicenter of the security system, this interface allows users to control settings, arm or disarm the system, and communicate with all connected devices. It is the point of integration for all sensors and cameras, processing data and executing programmed actions.
- Sensors and Detectors: These devices are the system’s eyes and ears, strategically placed throughout the property. They include door and window sensors, which alert the system to any unauthorized opening; motion detectors, which sense movement within a designated area; and glass break sensors, which detect the sound frequency of breaking glass.
- Surveillance Cameras: Offering both indoor and outdoor monitoring capabilities, cameras play a pivotal role in visual surveillance, allowing for real-time viewing and recording of the property’s perimeter and internal spaces. They can be crucial in both deterring potential intruders and providing evidence in the event of a security breach.
- Environmental Sensors: Expanding the system’s scope beyond security, these sensors detect environmental dangers such as smoke, fire, carbon monoxide, water leaks, and substantial shifts in temperature, providing an additional layer of safety to protect against non-intrusive threats.
- Access Control Systems: These systems manage entry to the property or specific areas within it. They can range from simple key fobs for arming or disarming the system to sophisticated biometric systems that restrict access based on unique physiological characteristics.
- Alarm Systems and Sirens: Serving as the immediate response mechanism to detected threats, these components signal an alert in the form of loud sirens or flashing lights, designed to notify occupants and possibly deter intruders.
- Communication Interfaces: Essential for alerting property owners and monitoring services to potential threats, these systems utilize cellular, Wi-Fi, or landline connections to ensure that the security system remains in constant communication with relevant parties, even in the absence of property occupants.
Understanding these components and their functions is crucial for anyone looking to implement, program, or update a security system, ensuring a personalized and effective security solution tailored to their specific needs and lifestyle.
Security System Features and Functionalities
When selecting or upgrading a security system, understanding the array of features and functionalities available is essential for tailoring the system to your specific preferences and requirements. Modern security systems offer a wealth of advanced capabilities designed to enhance protection, convenience, and user control. Among these features are:

- Remote Access and Control: Many security systems now offer the ability to control and monitor your home security remotely via a smartphone app. This feature allows homeowners to arm or disarm their system from anywhere, check the status of sensors, and view live camera feeds.
- Automation Integration: Integrating your security system with home automation devices brings convenience and efficiency to a new level. Set scenes or actions that automatically adjust lighting, climate control, and even lock doors when the system is armed or disarmed.
- Customizable Alerts: Customization of alerts and notifications is a key functionality. Users can set up real-time alerts for specific events, such as when a door is opened, motion is detected in a restricted area, or if environmental sensors trigger an alarm.
- Voice Control: Compatibility with voice-activated assistants like Amazon Alexa, Google Assistant, and Apple HomeKit enables users to control their security system with simple voice commands, adding an extra layer of convenience and accessibility.
- Geofencing: This feature uses the location of your smartphone to control your home security system automatically. For example, it can arm the system when you leave a designated area around your home and disarm it as you return, ensuring you never forget to set your alarm again.
- Video Analytics: Advanced surveillance cameras equipped with video analytics can distinguish between people, vehicles, and animals, reducing false alarms and focusing attention on genuine threats. Some systems can even recognize familiar faces or detect unusual patterns of activity.
- 24/7 Monitoring: Professional monitoring services offer round-the-clock surveillance of your security system, with trained professionals on hand to respond to alerts and notify emergency services if needed, providing an added layer of reassurance.
- System Health Checks: To ensure your security system is always functioning optimally, some systems feature regular automated health checks that monitor the status of connected devices and alert you to any issues that need addressing.

By taking advantage of these sophisticated features and functionalities, users can develop a comprehensive security system that not only protects against unauthorized access but also offers a degree of convenience and control that was once unimaginable.
Familiarization with Security System Terminology
Familiarization with the specific terminology used in security systems is essential for users to fully understand and effectively manage their security solutions. Terms such as “zone” refer to specific areas or sectors of a property that a security system monitors independently.
“Encryption” ensures that communications between your security devices and the control panel are secure and protected from unauthorized access. Understanding the difference between “wired” and “wireless” systems can influence the installation process and system maintenance. “Wired” systems are connected through physical cables, offering reliability but requiring more extensive installation, whereas “wireless” systems use radio frequency signals for communication, making them easier to install and update but sometimes subject to interference.
“Two-factor authentication” is another critical term, referring to an additional security layer that requires not only a password and username but also something that the user has on them, ensuring higher security levels. Grasping these terms can empower homeowners and business owners, enabling them to make informed decisions about their security system configuration, customization, and operation.
Assessing Security Needs and Requirements
Assessing your security needs and requirements is a vital step toward selecting the ideal security system for your home or business. This evaluation involves considering several factors that contribute to your overall security posture.

Firstly, identify the specific threats or vulnerabilities your property faces, such as burglary, vandalism, or environmental dangers like fire and floods. Understanding the local crime rates and potential natural disaster risks can also provide valuable insights into what security features are most necessary for your situation.
Next, evaluate the layout of your property, identifying key points of entry and areas that may be more susceptible to unauthorized access or require special attention, such as windows, garages, or secluded doors. The size and complexity of your property will influence the type and extent of the security system needed.
Consideration of your lifestyle or business operations is also essential. For households with children or pets, systems with advanced motion sensors that differentiate between humans and animals may be beneficial. Businesses handling sensitive information might prioritize systems with higher levels of encryption and data protection.
Lastly, assess your budget not just for the initial investment in the security system but also for ongoing expenses such as monthly monitoring fees, maintenance, or potential upgrades. Balancing cost with the level of security and functionality you require will help you make an informed choice that offers peace of mind and protection for your assets.
10 Methods How to Program a Security System
Method 1: Conducting a Security Assessment
Before programming a security system, conducting a thorough security assessment is essential. We’ll discuss how to identify vulnerabilities, assess risks, and determine specific security needs and requirements for the property.
Method 2: Accessing the Control Panel
Step-by-step instructions for accessing the security system control panel will be provided. We’ll cover the navigation of the control panel menu and user interface, as well as understanding control panel settings and configuration options.

Method 3: Adding and Configuring Sensors
Setting up door/window sensors for intrusion detection and configuring motion detectors for interior protection will be covered. Additionally, we’ll discuss programming other sensors and detectors such as smoke detectors and carbon monoxide detectors based on security needs.
Method 4: Setting Up User Codes and Access Control
Creating master codes and user codes for system arming and disarming will be explained. We’ll also cover configuring access control settings for different users or groups and establishing schedules and permissions for user access.
Method 5: Configuring Alarm Notifications and Alerts
Instructions for setting up alarm notification preferences, such as email, SMS, or phone call, will be provided. We’ll also discuss configuring alerts for specific events like intrusion, fire, or carbon monoxide detection and testing alarm notifications for proper functionality.
Method 6: Integrating Home Automation and Smart Devices
Exploring integration options with home automation devices like smart locks, lights, and thermostats will be covered. We’ll discuss programming automation rules and scenarios for enhanced security and convenience and configuring remote access and control of smart devices through the security system interface.
Method 7: Conducting System Tests
Guidance on conducting system tests to ensure proper functionality of sensors, detectors, and alarms will be provided. We’ll cover fine-tuning system settings and configurations based on test results and addressing any issues or discrepancies discovered during testing.
Method 8: Establishing Professional Monitoring Services
Exploring options for professional monitoring services and their benefits will be discussed. We’ll cover the process of setting up professional monitoring and the advantages of having a third-party monitor your security system.
Method 9: Creating a Maintenance Schedule
Instructions for establishing a maintenance schedule for regular system checks and updates will be provided. We’ll discuss implementing best practices for ongoing security system maintenance and optimization to ensure continued reliability and effectiveness.
Method 10: Implementing Security System Best Practices
Guidance on implementing security system best practices, such as keeping software up-to-date, securing access to the control panel, and regularly reviewing system logs, will be covered. We’ll discuss the importance of staying vigilant and proactive in maintaining the security of your system.
Conclusion
In conclusion, mastering the programming of a security system empowers homeowners and property managers to customize and optimize their security measures effectively.
By following the comprehensive guide provided, you’ve gained the knowledge and skills necessary to program a security system tailored to your specific needs and requirements. From configuring sensors and detectors to setting up user codes and access control, each step contributes to a robust security infrastructure capable of detecting and responding to potential threats.
Additionally, by integrating home automation and smart devices, you can enhance both security and convenience in your property. Remember to conduct regular testing, monitoring, and maintenance to ensure the continued reliability and effectiveness of your security system. Be sure to follow all instructions on how to program a security system carefully, and always consult an expert when in doubt.